security risks with outsourcing cloud computing services computer science homework help
This is a discussion question. No APA format needed but references are required.
Network Systems Design
Question A
What are some of the security risks with outsourcing cloud computing services to a third party organization and what are the methods to help counteract these risks?
Question B
What problems arise when organizations use a reactive method of intrusion detection and what are some requirements that can be added to a security policy to alleviate these problems?
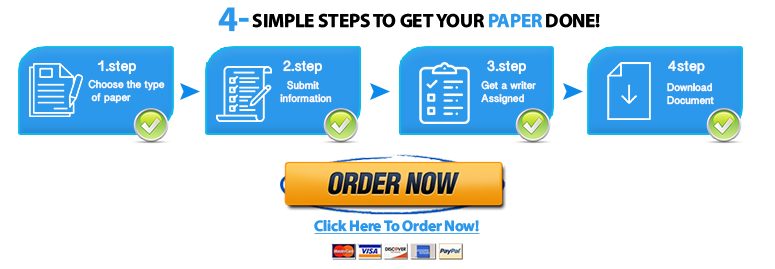
Do you need a similar assignment done for you from scratch? We have qualified writers to help you. We assure you an A+ quality paper that is free from plagiarism. Order now for an Amazing Discount!
Use Discount Code "Newclient" for a 15% Discount!
NB: We do not resell papers. Upon ordering, we do an original paper exclusively for you.