what is risk assessment 1
When it comes to IT security, you must do more than follow the examples of other companies, regardless of how successful they are. No two organizations will encounter exactly the same problems. The best approach to providing the best level of security is to conduct a risk assessment of your organization, identify what your assets are, what your threats are, and what the probability of the threats occurring may be. This analysis will allow you to create the network defense plan that is uniquely tailored to your organization and situation.
Conduct an inventory of devices within the chosen organization’s network using appropriate tools.
Provide a summary of the number of desktops, laptops, network printers, and servers.
Identify key assets
Assets also include records and sensitive information that requires special protection
Prioritize each assets or group of assets and assign a value to each
Create a subsection that will identify and describe the risks within the environment
Do not forget natural disasters
Include the likelihood that risk can occur
Provide a lists of the tools and methodology that you used to conduct the risks.
**References
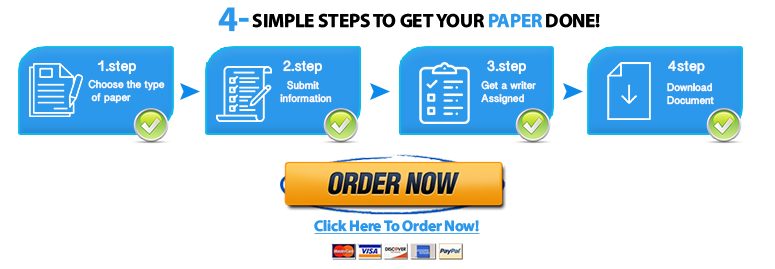
Do you need a similar assignment done for you from scratch? We have qualified writers to help you. We assure you an A+ quality paper that is free from plagiarism. Order now for an Amazing Discount!
Use Discount Code "Newclient" for a 15% Discount!
NB: We do not resell papers. Upon ordering, we do an original paper exclusively for you.